FIPS 140-2
|
Read other articles:

Disambiguazione – Piermarini rimanda qui. Se stai cercando altri significati, vedi Piermarini (disambigua). Giuseppe Piermarini Giuseppe Giorgio Pietro Baldassarre Piermarini (Foligno, 18 luglio 1734 – Foligno, 18 febbraio 1808) è stato un architetto italiano. Indice 1 Biografia 1.1 Giovinezza e formazione 1.2 Piermarini valente architetto 1.2.1 Accademia di Mantova e università di Pavia 1.2.2 Villa Reale di Monza 1.2.3 Palazzo Belgioioso 1.2.4 Teatro alla Scala 1.3 Ultimi anni ...
Este artigo carece de caixa informativa ou a usada não é a mais adequada. Esta página cita fontes, mas que não cobrem todo o conteúdo. Ajude a inserir referências. Conteúdo não verificável pode ser removido.—Encontre fontes: ABW • CAPES • Google (N • L • A) (Julho de 2010) Nota: Para o mineral, veja Calcedônia (mineral). Para outros significados, veja Calcedônia. Calcedônia, na Anatólia, durante as Guerra...

Neem het voorbehoud bij medische informatie in acht.Raadpleeg bij gezondheidsklachten een arts. Traditionele Chinese geneeskunde Naam (taalvarianten) Vereenvoudigd 中医 Traditioneel 中醫 Pinyin zhōngyī Jyutping (Standaardkantonees) zung1 ji1 Standaardkantonees Chóng Yíe HK-romanisatie (Standaardkantonees) Chung Yee Yale (Standaardkantonees) jung1 yi1 Sichuanhua Dzong Ie Chinese medicijnwinkel in Tsim Sha Tsui, Hongkong. Traditionele Chinese geneeskunde, ook bekend als Chinese geneesku...

Naval Facility Point SurShow map of CaliforniaShow map of the United StatesLocationMonterey County, California, United StatesNearest cityCarmel, CaliforniaCoordinates36°18′15″N 121°53′18″W / 36.30417°N 121.88833°W / 36.30417; -121.88833Area92 acres (37 ha)Established1957Governing bodyCalifornia State ParkNaval Facility Point SurNAVFAC Point Sur logoActiveJanuary 1958 - October 1984DisbandedOperations computerized and data transmitted to NAVFA...

シンガポール国会議事堂 概要用途 議事堂所在地 シンガポール座標 北緯1度17分21秒 東経103度51分01秒 / 北緯1.2891度 東経103.8504度 / 1.2891; 103.8504座標: 北緯1度17分21秒 東経103度51分01秒 / 北緯1.2891度 東経103.8504度 / 1.2891; 103.8504着工 1995年完成 1999年所有者 シンガポール政府テンプレートを表示 国会議事堂(こっかいぎじどう、Parliament House, S...

Tàu tuần dương Noshiro trong vịnh Tokyo, tháng 7 năm 1943 Lịch sử Nhật Bản Đặt hàng 1939Xưởng đóng tàu Xưởng hải quân YokosukaĐặt lườn 4 tháng 9 năm 1941Hạ thủy 19 tháng 7 năm 1942Hoạt động 30 tháng 6 năm 1943 [1]Xóa đăng bạ 20 tháng 12 năm 1944Số phận Bị máy bay Mỹ đánh chìm ngày 26 tháng 10 năm 1944 phía Nam Mindoro trong vùng biển Sulu11°42′B 121°41′Đ / 11,7°B 121,683°Đ...

The 2010 term of the Supreme Court of the United States began October 4, 2010, and concluded October 1, 2011. This was the sixth term of Associate Justice Samuel Alito's tenure on the Court. Samuel Alito 2010 term statistics 7 Majority or Plurality 6 Concurrence 1 Other 6 Dissent 1 Concurrence/dissent Total = 21 Bench opinions = 18 Opinions relating to orders = 3 In-chambers opinions = 0 Unanimous opinions: 0 Most joined by: Roberts (12) Least joined by: Kagan (4) Type Case Citation Issues Jo...

Pegaso Z-102 Pegaso Z-102 Touring Coupé. Datos generalesFabricante PegasoDiseñador Wifredo RicartFábricas La Sagrera, BarcelonaBarajas, MadridPeríodo 1951 – 1958ConfiguraciónTipo Automóvil deportivoCarrocerías Cupé dos puertas Descapotable dos puertasConfiguración Motor V8 delantero longitudinal, tracción trasera, transmisión de 5 velocidades manualDimensionesDimensiones 4.100 mm / 1.580 mm / 1.290 mm / 2.340 mmPeso 980 kgOtros modelosSucesor Pegaso Z-103[editar datos en Wik...

Sunni Islamic university in Iran The topic of this article may not meet Wikipedia's notability guidelines for companies and organizations. Please help to demonstrate the notability of the topic by citing reliable secondary sources that are independent of the topic and provide significant coverage of it beyond a mere trivial mention. If notability cannot be shown, the article is likely to be merged, redirected, or deleted.Find sources: Jamiah Darul Uloom Zahedan – news ·...

2014 soundtrack album by John PowellHow to Train Your Dragon 2Soundtrack album by John PowellReleasedJune 13, 2014Recorded2012–2014GenreFilm scoreLength1:11:23LabelRelativity Music GroupJohn Powell chronology Rio 2(2014) How to Train Your Dragon 2(2014) Pan(2015) Singles from How to Train Your Dragon 2 Into a FantasyReleased: June 9, 2014 How to Train Your Dragon 2: Music from the Motion Picture is a soundtrack album to the 2014 film How to Train Your Dragon 2, and was released by R...

2002 film by Andrzej Sekula Cube 2 redirects here. For the video game, see Cube 2: Sauerbraten. For the digital audio player, see Cube2. 60659 redirects here. For the ZIP Code, see North Park and West Ridge, Chicago. Cube 2: HypercubeTheatrical release posterDirected byAndrzej SekułaScreenplay bySean Hood[1]Ernie Barbarash[1]Lauren McLaughlin[1]Story bySean Hood[1]Produced by Ernie Barbarash Suzanne Colvin Starring Kari Matchett Geraint Wyn Davies Grace Lynn K...

Body which defines British electoral constituencies The boundary commissions in the United Kingdom are non-departmental public bodies responsible for determining the boundaries of constituencies for elections to the House of Commons.[1] There are four boundary commissions: Boundary Commission for England Boundary Commission for Scotland Boundary Commission for Wales Boundary Commission for Northern Ireland Each commission comprises four members, three of whom take part in meetings. Th...

Flag carrier of Albania Air Albania IATA ICAO Callsign ZB ABN[1] AIR ALBANIA[1] Founded16 May 2018 (5 years ago) (2018-05-16)Commenced operationsApril 2019 (4 years ago) (2019-04)[2]HubsTirana International Airport Nënë TerezaFleet size3Destinations9HeadquartersTirana, AlbaniaKey peopleSinan Dilek (CEO)Websitewww.airalbania.com.al Air Albania is the flag carrier of Albania.[3] The airline maintains its hub and company headquar...

This article is about the story compilation by Stephen King, Dan Simmons and George R. R. Martin. For the YA trilogy by L. J. Smith, see Dark Visions Trilogy. The Skin Trade redirects here. For other uses, see Skin Trade (disambiguation). Dark Love redirects here. For the 2010 Italian movie by Antonio Capuano, see Dark Love (film). Horror fiction compilation Dark Visions First edition (under original title)AuthorStephen King,Dan Simmons,George R. R. MartinOriginal titleNight Visions 5Cov...

This article needs additional citations for verification. Please help improve this article by adding citations to reliable sources. Unsourced material may be challenged and removed.Find sources: Burt Reynolds filmography – news · newspapers · books · scholar · JSTOR (September 2018) (Learn how and when to remove this template message) Burt Reynolds filmography Reynolds in Dan August (1972) Filmography: Feature films 145 Television films 13 Television s...

ConkyA typical Conky appearanceOriginal author(s)Brenden MatthewsStable release1.19.6[1] / 13 October 2023; 55 days ago (13 October 2023) Repositorygithub.com/brndnmtthws/conky Written inC, C++Operating systemLinux, FreeBSD, and OpenBSDTypeSystem monitorLicenseGPL and BSD licenses[2]Websitegithub.com/brndnmtthws/conky Conky is a free software desktop system monitor for the X Window System. It is available for Linux, FreeBSD, and OpenBSD.[3] Conky is ...

County in Ningxia, People's Republic of ChinaTongxin 同心县طْوثٍ ثِيًاTungsinCountyTongxin in WuzhongWuzhong in NingxiaCoordinates (Tongxin government): 36°57′16″N 105°53′43″E / 36.9544°N 105.8954°E / 36.9544; 105.8954CountryPeople's Republic of ChinaAutonomous regionNingxiaPrefecture-level cityWuzhongArea • Total4,433.34 km2 (1,711.72 sq mi)Population • Total318,153 • Density72/km2 (190/sq...
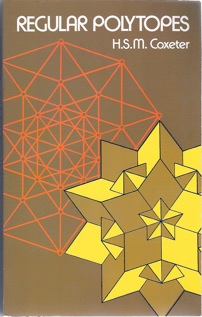
Geometry book Cover of the Dover edition, 1973AuthorHarold Scott MacDonald CoxeterLanguageEnglishSubjectGeometryPublished1947, 1973, 1973PublisherMethuen, Pitman, Macmillan, DoverPages321ISBN0-486-61480-8OCLC798003 Regular Polytopes is a geometry book on regular polytopes written by Harold Scott MacDonald Coxeter. It was originally published by Methuen in 1947 and by Pitman Publishing in 1948,[1][2][3][4][5][6][7][8] with a secon...

Perang Tiongkok-SikhJenderal Zorawar Singh (1786-1841)TanggalMei 1841 – Agustus 1842LokasiTibet dan LadakhHasil KebuntuanPerubahanwilayah Status quo ante bellumPihak terlibat Dinasti Qing Kemaharajaan SikhTokoh dan pemimpin Meng BaoHaipu Sher Singh, Maharaja Punjab Zorawar Singh Kahluria †Kekuatan Tidak diketahui Tidak diketahui Perang Tiongkok-Sikh Hanzi tradisional: 森巴戰爭 Hanzi sederhana: 森巴战争 Makna harfiah: Perang Dogra Alih aksara Mandarin - Hanyu Pinyin: Sēnbā Z...

English actor (1946–2016) Not to be confused with Alan Richman. Alan RickmanRickman in 2011Born(1946-02-21)21 February 1946Acton, Middlesex, EnglandDied14 January 2016(2016-01-14) (aged 69)London, EnglandAlma materRoyal Academy of Dramatic ArtOccupationsActordirectorYears active1974–2016WorksFull listPolitical partyLabourSpouse Rima Horton (m. 2012)AwardsFull list Alan Sidney Patrick Rickman (21 February 1946 – 14 January 2016) was an E...

